Contents:
- Why Your Company Needs Anomaly Detection
- Anomaly Detection in Business, What Is It?
- Types of Anomalies
- Anomaly Detection for product quality in manufacturing using Supervised Learning
- Time Series Anomaly Detection in Telecom or Retail
- Anomaly Analysis System in Logistics and Supply Chain Area
- Buying a ready-made system or creating your own: how to choose
- Building Your Own AD System: Pros and Cons
- SaaS Anomaly Detection Systems: Advantages & Disadvantages
- Consultation
Why Your Company Needs Anomaly Detection
Every business produces and stores considerable amounts of data, regardless of its domain. Whether it deals in Retail, Fintech, eCommerce, or Manufacturing, it operates hundreds of thousands of units of data.
Usually, all these data are hosted in the internal systems, being processed by in-house analysts or automatically using internal or external analytics dashboards. Businesses rely on this data to make the right business decisions, leveraging all the insights, numbers, and stats obtained through data analysis.
Using ML and AI solutions, data analysts can enable such basic processes as automated data processing, predictions, clustering, and others. One of the widely used methods is called Anomaly Detection and it allows you to look at your business from a completely different angle.
The goal of anomaly detection is to provide comprehensive insider information about your business or data. It helps business owners take a rational look at their business and analyze it both from the inside and outside, and find things they might have missed or simply not noticed before, providing a fast automated alternative to manual anomaly detection techniques.
Anomaly Detection in Business, What Is It?
Anomaly detection is a method of identification of any deviations from the norm in your data or products. Anomaly detection systems help reveal whatever is out of the ordinary in your dataset: points, patterns or tendencies. The anomaly detection technique was created to help solve the problems which in the past had been solved by means of data clustering and classification.
Types of Anomalies
There are 3 types of anomalies which you will encounter in your work, and the image below illustrates the difference between them:
- Contextual anomalies
- Conditional outliers
- Collective outliers

Anomaly Detection for Product Quality in Manufacturing Using Supervised Learning
Modern factory managers don’t have to rely on their multiple departments to do the necessary monitoring of the manufacturing systems. The product quality and performance are crucial and as a manager or business owner, you have to make sure the whole manufacturing process is smooth and flawless – from the very rollout to functionality updates.
Using this approach, manufacturing plants can detect potential problems and get answers to the following questions:
- In which place and when did the abnormal behavior take place?
- When and where did the anomaly occur or will occur?
- What are the recommendations for the necessary measures? Is it time to purchase new equipment?
- What were the underlying causes of this abnormal result?
Real-life examples:
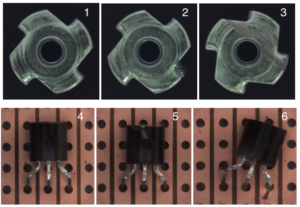
Manufacturing is a very dynamic industry, thousands of products are created every day. Still, we often can see that factories employ the whole departments of people who visually check products for defects, such as damages like on images 2 and 4, scratches (image 3) or the wrong location of the detail (image 6).
The maintenance of a quality department like this can cost hundreds of thousands of dollars per year, and it still leaves room for human errors, when workers skip defective details or goods.
Where human labor can’t cover 100% of cases, Machine Learning, Supervised Learning comes to the rescue. This is how we’re able to teach the system to do the exact same thing as humans would (sort, review, find defects), but better, faster, because unlike humans, the machine does not get tired and doesn’t lose focus. Of course, it is not perfect either, but it can cover the larger chunk of work and only turn to human’s indisputable cases, where it needs human oversight.
Such a system would allow to reallocate 50-70% or even 90% of staff, assigning them to more important tasks, thus optimizing the company’s QA expenses considerably.
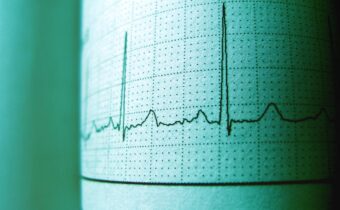
Time Series Anomaly Detection in Telecom or Retail
In Retail and Telecom, everything happens fast, often decisions have to be made on the spot. In order to make the right decision managers need to get a grasp on what is going on right now or what was happening during a certain period of time in the past. Here’s when Time Series Anomaly Detection comes on stage.
Such systems are capable of analyzing the work of a system, rapidly detect errors and warn about them, so that the company can take the right steps and warn the users about the possible system failures.
The system also helps to analyze the workload of the support team and ensure the quality interaction between the support team and the users. On the prevention side, it monitors the equipment and its performance assisting with timely detection of potential causes for failures or errors, which can cost the company tens of thousands of dollars.
Here are a few examples of insights that the Anomaly Detection method can provide for the Retail industry:
- Monitoring the inventory dynamics (sudden decreases in the stock of goods). Here we described our experience with ML-based sales prediction.
- Detecting changes and patterns in the Sales volume (e.g. seasonal or other peaks in demand)
- EBT transactions data processing
The Anomaly Detection method is a useful tool to optimize the company’s expenses, automate manual routine processes, and provide helpful information about the company, which allows making smarter business decisions.
Anomaly Analysis System in Logistics and Supply Chain Area
Imagine a Machine Learning-based system that helps companies in Logistics and Transportation monitor their vehicles and spot potential issues on the road right away. The Anomaly Analysis System consists can determine whether there is anything out of the ordinary in the behavior of the vehicle, the state of the engine RPM, fuel consumption, transmission,
GPS and Maps, helping build further routes and calculate the time for their passing.

The system can analyze such anomalies as:
- Anomalies in the route maps, the absence of the road, outdated maps, unpredicted ascents or descents.
- In case the GPS tracker does not work properly, the system can let you know whether the vehicle is moving and whether it’s following the right route, or moving up or down.
- The vehicle data, fuel consumption, transmission, speed, revs, etc. This data can show whether the driver moves in the right way on this part of the road, whether there are any anomalies in the work of an engine, which can potentially cause breakdowns or failures.
Combining these 3 categories we can build an ML system that can analyze the data and detect potential anomalies, telling us whether the route is correct and whether the behavior of the vehicle’s engine corresponds to its location and timing.
Buying a Ready-Made System or Creating Your Own: How to Choose
First, clearly state your reason for investing in anomaly detection research. This method requires careful preparations, time, and money. If you clearly understand the need you’re trying to solve with this technique, you will be able to achieve maximum value and unlock the full potential of anomaly detection.
The task is quite widespread and multiple companies have researched it, which resulted in the creation of numerous SaaS systems, ready to process your data at once. So the question is: should you invest in developing your own anomaly detection system or rather find an existing alternative and pay for the subscription. Here are the factors to consider:
- Your budget. How much time and money are you willing to invest?
- What data do you have for analysis, their volume, quality, and how ready they are for analysis. How confidential are these data? Can you share them with 3rd party systems?
- The size of your company, your ability to develop and maintain a proprietary system, or your willingness to outsource this task.
- Do you plan to scale or change the flow of the structure of your data?
After answering these questions you’ll be able to find the optimal solution for your business.
Building Your Own AD System: Pros and Cons
Advantages:
- The system is configured to work with your problem and process your data. Data is the DNA of your business, it is unique for each business and the fact that the system is so customized can sometimes prove invaluable.
- Your business data are protected and secure, they remain with you, no need to disclose them to 3rd parties.
- You are able to manage the development process, influence the updates.
- If your business reaches a certain scale, then the product will pay off faster than a 3rd party solution would. You don’t depend on any external company.
Aspects to pay careful attention to:
- The initial investment. For starters, you’ll have to invest more money to develop a proprietary system than you would invest in a ready-made solution.
- Development and implementation take time.
- It is necessary to build a development team or find the right software engineering vendor.
Conclusion: This approach is perfect for companies who clearly understand what kind of data they have and what value they want to receive from them. Such companies have long-term goals, they are ready to invest in the future and think big. This method won’t work for short-term goals or the validation of hypotheses; it is not the right choice if what you need is to present a prototype to investors or the board to get funding. Working with ready-made solutions might be a better option here.
SAAS Anomaly Detection Systems: Advantages & Disadvantages
Advantages:
- You can receive the first results faster. You skip the development stage, you only have to prepare the data and implement the chosen system.
- The price – you don’t have to invest in the creation of a system, so this option is definitely cheaper than the one above.
- The speed – you get results fast and they can be processed right away.
Things to consider and watch out for:
- Here you are entrusting your sensitive data to 3rd parties.
- Such systems rarely fit like a glove to the needs of your business, here it is you who has to adjust, and the results might not meet your expectations.
- Unsuitable in the long run – you depend too much on 3rd parties, which makes your data and your business vulnerable.
Conclusion: This approach will work for companies with relatively small budgets, or the ones looking to validate their ideas, present something to potential investors, and attract funding for building their own systems in the future. It is important to understand here that such systems are not 100% secure and you risk compromising your data.
The anomaly detection method is a powerful force that can significantly enhance your business, and drive it forward. You can start using modern AD systems immediately, you only have to have the right data. This method proved invaluable in the automation of manual labor, providing managers and business owners with unique information about various aspects of their business. Before resorting to this method, we strongly recommend you to consider the needs of your business and find the optimal way to apply this technique, and the right approach, which will fit your budget, your timelines and provide maximum value.
If you still have questions or doubts about your business data, or you are in need of expert consultation, we will gladly advise you and help you get started. Mindcraft has hands-on experience in designing, developing, and implementing Anomaly Detection systems for businesses across industries, we are qualified to help your company benefit from this technique as well. To receive a consultation, contact us at team@mind.local.
Also Thanks for authors
Image from researchgate
Data Set Link – Mvtec